The number of DDoS attacks declined 13% in the first half of 2018 compared the same period last year. While not a huge percentage, the report suggests more than 400,000 DDoS attacks are recorded every month worldwide.Simply so, how many DDoS attacks are there in 2019?
2, 2018 and May 4, 2019, Akamai observed more than 800 DDoS attacks against the financial industry — a number that represents more than 40 percent of all unique DDoS targets they observed during that time. 14.
Secondly, what is the most recent DDoS attack? 5 of the Most Famous Recent DDoS Attacks
- GitHub (February, 2018) A popular online code management service used by millions of developers, GitHub is used to high traffic and usage.
- Dyn (October, 2016)
- BBC (December, 2015)
- Spamhaus (March, 2013)
- Bank of America/JP Morgan Chase/US Bancorp/Citigroup/PNC Bank (December, 2012)
Correspondingly, how common are DDoS attacks?
How common are distributed denial of service attacks? According to that company's press release, 35 percent of those companies surveyed said that they had experienced a DDoS attack in the previous 12 months. The most common cyberattacks were malware (53 percent) and viruses (51 percent).
Where do most DDoS attacks come from?
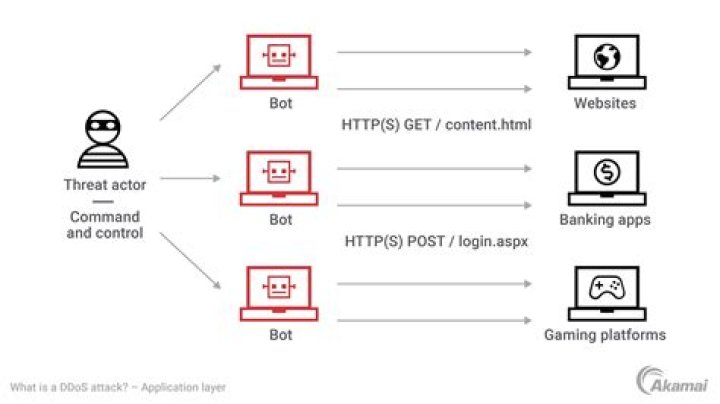
Typically, DDoS attackers rely on botnets – collections of a network of malware-infected systems that are centrally controlled. These infected endpoints are usually computers and servers, but are increasingly IoT and mobile devices.
Can you DDoS Google?
This likely is actually impossible. Google has so many thousands or maybe millions of beefed-up servers that it is probably nigh-impossible to DDoS them. You would need so many computers to do this that the costs would become impossible to calculate. Actually, your ISP will probably go down before Google ever does.What is the best DDoS method?
Following are the methods of doing DDoS attacks: - UDP flood.
- ICMP (Ping) flood.
- SYN flood.
- Ping of Death.
- Slowloris.
- NTP Amplification.
- HTTP flood.
What was the first DDoS attack?
The first documented DoS-style attack occurred during the week of February 7, 2000, when “mafiaboy,” a 15-year-old Canadian hacker, orchestrated a series of DoS attacks against several e-commerce sites, including Amazon and eBay. Distributed DoS (DDoS) attacks are a special kind of hacking.How do you protect against DDoS?
7 Tips for Defending Your Network against DDoS Attacks - Document your DDoS resiliency plan.
- Recognize DDoS attack activity.
- Don't assume that only large-scale, volumetric attacks are the problem.
- Don't rely on traffic monitoring or thresholds.
- Don't rely on an IPS or firewall.
- Engage with a mitigation provider.
- Pair time-to-mitigation with successful attack protection.
What is Mirai attack?
Mirai (Japanese: ??, lit. 'future') is a malware that turns networked devices running Linux into remotely controlled bots that can be used as part of a botnet in large-scale network attacks. It primarily targets online consumer devices such as IP cameras and home routers.How many DDoS attacks occur every day?
According to a SecurityWeek article, “By combining the direct attacks with the reflection attacks, the researchers discovered that the internet suffers an average of 28,700 distinct DoS attacks every day.How do DDoS attacks happen?
A distributed denial-of-service (DDoS) attack occurs when multiple systems flood the bandwidth or resources of a targeted system, usually one or more web servers. Such an attack is often the result of multiple compromised systems (for example, a botnet) flooding the targeted system with traffic.What is difference between DoS and DDoS?
The Difference Between DoS and DDos Attacks The DoS attack typically uses one computer and one Internet connection to flood a targeted system or resource. The DDoS attack uses multiple computers and Internet connections to flood the targeted resource.What is the biggest DDoS attack?
The biggest DDoS attack to date took place in February of 2018. This attack targeted GitHub, a popular online code management service used by millions of developers. At its peak, this attack saw incoming traffic at a rate of 1.3 terabytes per second (Tbps), sending packets at a rate of 126.9 million per second.Can you trace a DDoS attack?
No. You cannot trace back a DDos Attack. Which means attack is from different end.Can a vpn be Ddosed?
When you use a VPN such as Private Tunnel, your internet traffic is channeled through an encrypted pathway to one of our external servers, which hides your true IP address. By shielding your IP address, your internet connection is protected from being a target of a DDoS attack.How long do DDoS attacks last?
24 hours
Is DDoS illegal?
DDOS refers to a Distributed Denial of Service. While some observers defend DDOS attacks as a form of mass demonstration against an offending website, it is illegal under the Federal Computer Fraud and Abuse Act. Violators are subject to prison sentences of up to 10 years and a fine of up to $500,000.Is DDoS easy?
A distributed denial of service attack (aka DDOS) is very easy, and is in fact widely considered one of the easiest blackhat activities to do. A distributed denial of service attack (aka DDOS) is very easy, and is in fact widely considered one of the easiest blackhat activities to do.Can DDoS attacks steal information?
DDoS attacks cannot steal website visitors information. The sole purpose of a DDoS attack is to overload the website resources. However, DDoS attacks can be used as a way of extortion and blackmailing. For example, website owners can be asked to pay a ransom for attackers to stop a DDoS attack.What is Teardrop attack?
A teardrop attack is a denial-of-service (DoS) attack that involves sending fragmented packets to a target machine. Since the machine receiving such packets cannot reassemble them due to a bug in TCP/IP fragmentation reassembly, the packets overlap one another, crashing the target network device.Is Ddosing on Xbox illegal?
This is the part of the story that those who say "A DDoS is NOT ILLEGAL!" fail to grasp. Writing malevolent code that infects and invades another person's computer, and then makes that computer a chain in the botnet army of DDoS attacks IS illegal.